From misclick to leadership crisis: Lessons from the MoD data leak for cyber governance
Executive Summary: What decision-makers need to know immediately
System errors instead of human error:
A single misclick is never the cause, but rather a symptom. TheBritish Ministry of Defense caseshows that lack of controls, inadequateGovernanceand ineffective awareness programs are a ticking time bomb in every company.
Secrecy is not a strategy:
The attempt to keep the incident secret through a court injunction ("super-injunction") did not contain the crisis, but rather exacerbated the governance failure and prevented independent oversight. Transparency is now a risk management requirement.
The responsibility is at the C-level:
New regulations likeNIS2,DORAand others place responsibility for cyber risk management and transparent reporting obligations directly on the boards of directors and management. Ignorance no longer protects against consequences.
Human-Centric Security is the only way:
Effective security protects people from making mistakes rather than punishing them for them. Smart, contextual controls (e.g. “just-in-time” alerts) are more effective than any standard annual training.
The anatomy of a preventable disaster
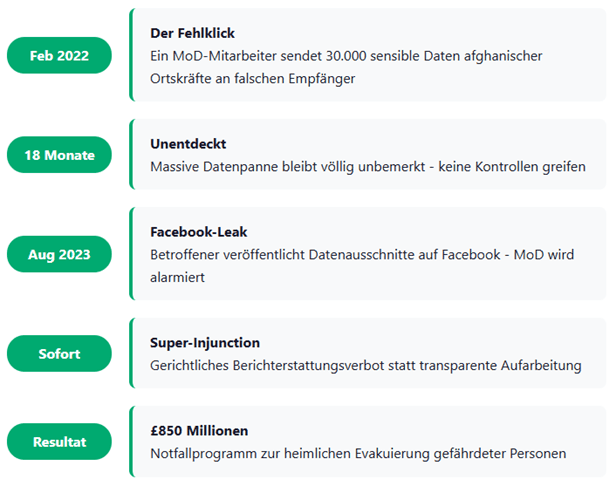
In February 2022, an employee of the British Ministry of Defense (MoD) sends an email. A fatal error in the recipient line means that a file containing over 30,000 highly sensitive applications from Afghan local staff who had worked with British troops is sent to an external, unauthorized recipient.
What follows is a lesson in catastrophic crisis management:
18 months undetected:
The massive data outflow went unnoticed for over a year and a half. It was only when a person affected published excerpts of the leaked data on Facebook in August 2023 that the MoD was alerted.
Silence instead of enlightenment:
Instead of acting transparently, the government enforces a "super-injunction" - a far-reaching, court-ordered ban on reporting. The reason: protection of up to 100,000 vulnerable people whose lives are at stake.
Cost explosion in secret:
Behind the scenes, an emergency program worth over £850 million is being set up to secretly bring those at risk to safety. The cost of an individual's mistake explodes.
This incident is more than a technical glitch. It is a strategic governance disaster that raises a central question:
This article goes beyond the usual analysis. We deconstruct the three fundamental levels of failure - awareness, governance and controls - and provide a strategic roadmap for decision-makers to prevent similar disasters at home.
Level 1: The Awareness Dilemma - Why Your Security Training Is Failing
The root of the MoD incident was a classic human error, but it represents only the end of a chain of systemic failure. The real weakness lies in the assumption that annual compliance training is an effective line of defense.
What went wrong in the MoD case:
Classic operating error:
A wrong recipient due to autocomplete or carelessness - a risk that exists thousands of times every day in every company.
Lack of situational awareness:
The dispatch of 30,000 data sets should have immediately raised alarm bells. This indicates a lack of awareness about how to handle mass data.
Culture of silence:
The fact that the incident was not reported internally or detected through monitoring for 18 months reveals a massive gap in security culture and monitoring processes.
Best practices for a human-centered safety culture:
An effective awareness strategy is not an annual event, but rather a continuous process that is integrated into daily operations.
Contextualized micro-training:
Replace one-hour, annual training sessions with 5-10 minute, role-specific learning sessions. An HR employee needs different scenarios than a developer. Use real, anonymized incidents from your company or industry for maximum relevance.
Behavioral incentives & just-in-time controls:
Integrate intelligent warning systems. A pop-up like "You are about to send a file containing 30,000 records to an external recipient. Please confirm the purpose and re-verify the recipient" could have prevented the MoD incident. An automatic 2-minute send delay for external emails gives employees a chance to correct errors.
Measurable effectiveness instead of participation rates:
Measure what matters. Instead of pure training participation rates, focus on KPIs such as “Mean Time to Report” (MTR), which is the average time it takes an employee to report a suspicious incident. Run simulated data handling exercises, not just phishing tests.
Level 2: The Governance Vacuum - When silence is more expensive than transparency
The MoD's response to the incident reveals a deep governance problem. The attempt to maintain control through secrecy created an oversight gap - a vacuum of accountability that encouraged bad decisions.
Lessons learned from crisis response:
Delayed disclosure increases risk:
In a world of NIS2, DORA, etc., late or opaque reporting is no longer an option. It increases legal, financial and reputational risk exponentially. The responsibility lies directly with management.
Lack of independent control:
The secrecy prevented scrutiny by parliament or independent oversight bodies. Without this control, costs and risks could escalate uncontrollably.
How to establish crisis-proof cyber governance:
Governanceis the strategic answer to the question: “Who is responsible if something goes wrong?”
Implement a Board-Level Cyber Governance Framework:
It is not without reason that the new NIST Cybersecurity Framework (CSF) 2.0 introduces the "GOVERN" function as a central pillar. Clearly define the company's risk appetite, assign responsibilities (data owner, data steward) and ensure that the board understands and supports this strategy - the “tone from the top” is crucial.
Conduct regular executive cyber risk reviews:
The CISO should present the board with a quarterly heatmap of the top 5 cyber risks - linked to the potential impact on finances, reputation and, as in the MoD case, on human lives (ESG factor).
Define a clear Incident Escalation & Disclosure Policy:
Set thresholds: When exactly do legal, communications, board and regulators need to be informed? In the event of a crisis, a clearly defined process takes the pressure off the decision and prevents panic reactions.
Level 3: The Control Deficit - Technology that values people
Even the best awareness and governance are toothless without technical and organizational controls that prevent errors or minimize their impact.
The technical and organizational weak points:
Missing outbound controls:
Sending a file containing 30,000 sensitive records should never have left the corporate network without being blocked or submitted for approval.
Insufficient logging & detection:
A detection time of 18 months is unacceptable. It points to a fundamental failure in monitoring data leaks.
The modern control stack for emergencies:
Modern controls are not designed to hinder employees, but rather to protect them from mistakes.
Organizational guidelines:
Implement a clear **Data Classification & Handling Standard**. Define which data can be stored and transferred and how. Introduce a four-eyes principle for the export of mass data and regularly check access rights.
Data Loss Prevention (DLP):
Modern DLP solutions work context-based. They not only recognize credit card numbers, but also unusual amounts of personal data and can automatically block sending or start an approval workflow.
Smart Email Security:
Tools that warn against sending to external domains (protection against autocomplete errors) and force encryption are now standard.
User & Entity Behavior Analytics (UEBA):
These systems learn the normal behavior of users and detect anomalies - such as an employee suddenly downloading or sending 30,000 records by an employee who would never normally do so.
Your Next Step: 5 Questions Your Board Needs to Ask This Week
The MoD case is a dire warning. Don't wait for your own crisis. Use these insights to proactively strengthen your resilience.
Start with these questions at your next board meeting or CISO meeting:
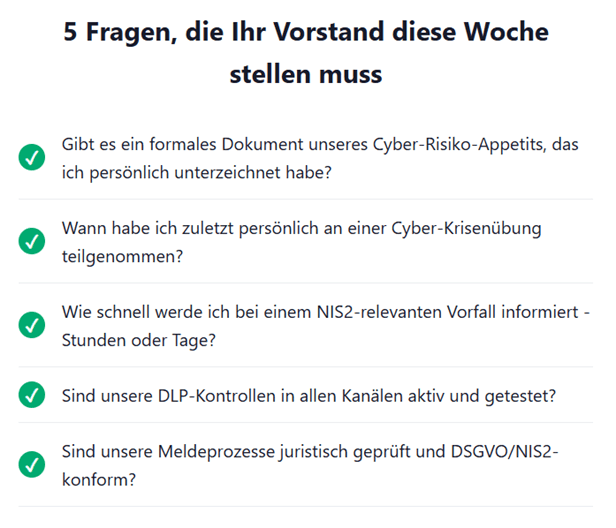
For the board/management:
1. Risk acceptance:
Is there a formal document that defines our risk appetite for cyber threats that I have personally signed?
2. Crisis preparation:
When was the last time I personally participated in a crisis management exercise for a major data incident?
3. Information speed:
How quickly will I be notified in the event of a potentially ""significant" (in the sense of NIS2) data breach - in hours or days?
For the CISO / Information Security Officer:
4. Effectiveness of controls:
Are our DLP policies not only active in all relevant channels (email, cloud, endpoints), but also tested and effective? What is our average time to detect (MTTD) of a data leak?
5. Legal certainty in an emergency:
Are our internal reporting and disclosure processes legally audited and in line with the new, strict deadlines of NIS2, DORA and the GDPR?
Conclusion
The answers to these questions will show you whether you're leading an organization that's primed for human error - or one that's waiting to become the next cautionary tale.
ADVISORI supports you with tailor-made solutionsSecurity awareness– individually for each company.
Follow us for more exciting insightsLinkedIn.
Next step: Free initial consultation
Would you like to set up governance structures optimally? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Related articles
Continue exploring with related insights from our experts.

Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.

Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.

Security Awareness Training: Building Effective Programs and Measuring Impact
The human layer remains the weakest link in cybersecurity. This guide covers how to build an effective security awareness program, run phishing simulations, design role-based training, and measure whether your program actually reduces risk — with benchmarks and KPIs.