NIS 2 training requirement: Three strategic competencies for management
Executive summary:
- Responsibility:Management has legal responsibility for implementing and monitoring cybersecurity measures. If you culpably breach your duty, you may face immediate and serious consequences.
- Three NIS-2 core competencies:To avoid liability, management must have knowledge and skills in theIdentification and assessment of risks, theRisk management practicesas well as theAssessment of their effectsaccess the services.
- Training requirement:Management of particularly important and important facilities mustregularlyParticipate in training, with the BSI recommending at least an interval of every three years.
- Strategic focus:Cybersecurity must be an integral part of the company's operations and risk management.
1. The strategic change: Why cybersecurity is a matter for the boss
The implementation of the NIS 2 Directive through the NIS 2 Implementation Draft (BSIG-E) significantly increases the requirements for companies. ForDecision makers (managers, VPs, CFOs, CTOs, managing directors)is crucial: Cybersecurity is no longer just a job for the IT department.
The legal basis (§ 38 BSIG-E) obliges the management of particularly important institutions and important institutions to implement the necessary risk management measures and to actively monitor compliance with them.If management culpably violates these obligations, they are liable for the damage caused in accordance with the rules of corporate law applicable to the legal form of the company.
In order to meet this enormous responsibility and minimize liability risks, the law provides for a separate training requirement for management. In its preliminary handout, the Federal Office for Information Security (BSI) has explained what content and ambition these training courses must meet in order to meet the legal requirements.
The role of the BSI guidelines
The BSI handout serves asfirst assistancein order to correspond to the BSI's understanding of the scope of training in accordance with Section 38 Paragraph 3 BSIG-E. Training courses that only focus on risk management measures are not rated as sufficient by the BSI because the three required aspects are inextricably linked.
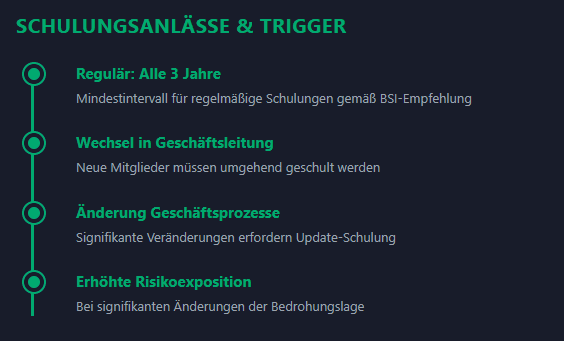
Training must take place regularly. The following applies as orientation:at least every three years. Reasonable reasons for a deviation or shortening of this minimum interval are:
- Change in management
- Significant changes in business processes
- Significant changes in risk exposure
The legislator does not set any rigid requirements for the duration, but assumes that the training courses average half a day (four hours), although the actual duration can significantly exceed four hours depending on the risk exposure.
2. The Deep Dive: The three NIS-2 core competencies
Management must be equipped with sufficient knowledge and skills in at least the following three interrelated areas:
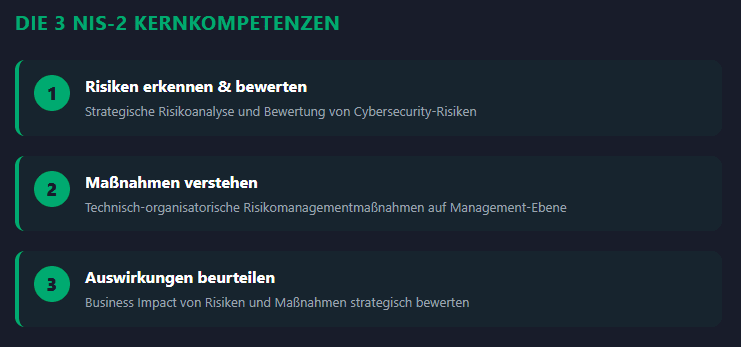
2.1 Core competency 1: Strategically identify and evaluate risks (risk analysis)
Management must be able to participateParticipate in the assessment of cybersecurity risksand to assess these sensibly in order to be able to take appropriate measures. It's not about technical depth, but about strategic classification.
What management should understand:
- Meaning, goals and central concepts of risk management as a systematic process.
- The risk management process in its components (analysis, evaluation, treatment, etc.).
- The identification ofassets(physical, digital, human, procedural, intangible).
- The basic concepts of risk assessment:
- Probability of occurrence.
- Extent of damage.
- Risk acceptance.
- Non-technical risks(e.g. due to human error, supply chain problems or organizational weaknesses) are part of the risk assessment.
- The possible types of damage (financial, reputational, operational, legal). The risk assessment must always take into account economic, legal and reputational consequences.
2.2 Core Competency 2: Understand risk management measures at management level
Management must be familiar with technical and organizational risk management measures. At least they have toMinimum requirements from Section 30 Paragraph 2 BSIG-Ebe conveyed. This is the understanding of theMode of actionandbusiness impactin focus, not the deep technical implementation.
What management should know:
- The legally specified minimum measures and their importance for your own institution.
- Risk management strategies (avoidance, mitigation, transfer, acceptance). Important: Transfer and acceptance are for important and particularly important facilitiesrather unacceptable.
- Basic principles and objectives of risk reduction measures.
- Measures mustState of the artcomply andproportionatebe.
- The effects of technical and organizational measures on business processes and theResilienceof the facility.
2.3 Core competency 3: The strategic assessment of the effects (business impact)
The combination of knowledge from risk identification and understanding of measures is crucial in order to achieve thisAssess the impact of risks and risk management measures sensiblyto be able to. Simply imparting knowledge is not enough.
What management should be able to judge:
- The impact of certain risks on theAvailability, integrity and confidentialityof the services provided.
- The potential oneseconomic, legal and reputational consequencesinadequate risk treatment.
- How preventative and reactive measures affect operational processes andService continuityimpact.
- Dependencies and domino effectsbetween IT systems, processes and services.
- Cybersecurity risks must be classified as business risksto make management decisions.
- The impact of inadequate implementation of risk management measures:
- Regulatory measures.
- Liability risks.
- That sufficientResources (budget, personnel)must be provided for the implementation of risk management.
3. Action-Oriented Conclusion
The NIS 2 directive unequivocally shifts cybersecurity responsibility to the senior management level.In order to minimize personal liability and strategic risks, regular, targeted training for management is essential.
Make sure:
- That your training courses completely cover the three core areas (risk analysis, measures, effects) - a focus solely on technical measures is not sufficient.
- Having in-house experts complement specific content tailored to your facility to maximize the effectiveness of the training.
- That you use scenarios, exercises and case studies to test your entrepreneurial decision-making and assessment skills and not just impart theoretical knowledge.
The training requirement is your strategic opportunity to anchor cybersecurity as a critical competitive advantage and to ensure the long-term resilience of your organization.ADVISORYactively supports you in planning, implementing and documenting the training measures.
Next step: Free initial consultation
📖 Also read:NIS2: How leaders use delay to turn risk into competitive advantage
📖 Also read:NIS2: How leaders use delay to turn risk into competitive advantage
Do you want to complete your NIS-2 registration? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Related articles
Continue exploring with related insights from our experts.
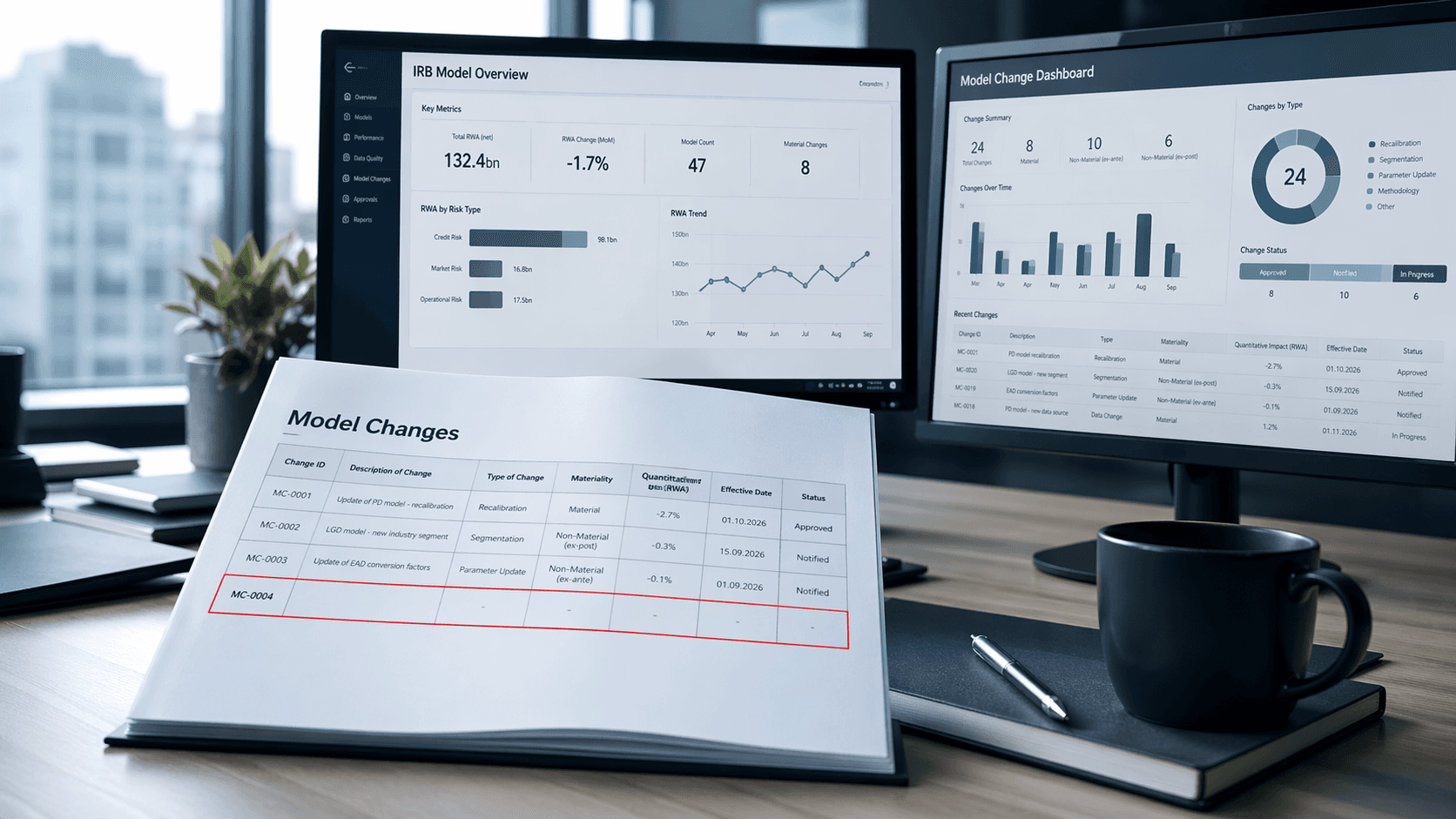
Less & Faster IRB Model Changes — What Actually Changed (and Why It Matters)
How the new IRB rules transform many previously time-consuming model changes into simple notifications—thereby drastically shortening approval times and significantly accelerating implementation

Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.

Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.