Private 5G networks: security, regulations and funding at a glance
Private 5G networks: security, regulations and funding at a glance
Introduction: Why private 5G networks?
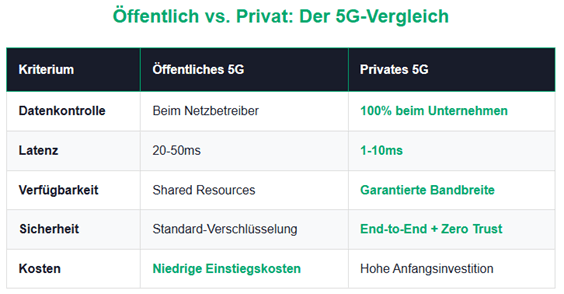
Private 5G networks give companies the opportunity to build high-performance, independent network infrastructures - with maximum control over data, speed and security. Whether Industry 4.0, networked logistics, energy or defense: the technology is a game changer. But with the advantages, the requirements for security, compliance and infrastructure also increase.
How do private 5G networks work?
A private 5G network is operated by a company itself, usually on the basis of frequencies assigned by the Federal Network Agency. It includes:
- Own base stations & core networks
- Dedicated spectrum(e.g. 3.7-3.8 GHz in Germany)
- Edge computingfor local data processing
- Isolation from the public network
The range of such a network is i. d. Usually limited locally (e.g. factory premises, campus), but in certain cases can be expanded to cover several square kilometers. The typical onedata rateis 100 Mbit/s up to the Gbit range with low latency (1-10 ms).
Security aspects: What do providers and users have to consider?
Provider obligations
- Zero trust security modelimplement
- End-to-end encryption(e.g. TLS, IPSec, AES-256)
- Intrusion detection & monitoring(e.g. SIEM)
- Network segmentation & firewalling
- Physical securityof infrastructure
User obligations
- Secure devices & authentication
- Separation of critical systems
- Awareness & Trainingof the employees
- Regular penetration testingand updates
Data protection & compliance
Private 5G networks mustGDPR compliantoperated, especially with personal data:
- Data minimizationand memory limitation
- Transparent access controls
- Loggingand auditability
- Local data processingthrough edge computing
Also other regulations (IT Security Act 2.0,BSI specifications) must be taken into account.
NIS2 & CRA: Who is affected and what does that mean?
NIS2
- Providers of private 5G networksare considered operators of critical communications services - they must present comprehensive security concepts, report incidents and demonstrate high cyber resilience.
- Users covered by NIS2(e.g. critical infrastructure), must also design and control their use securely.
- If theUser does not fall under NIS2, general due diligence and industry-specific standards apply (e.g. ISO 27001).
CRA (Cyber Resilience Act)
- Manufacturers and suppliersof 5G components must be included in products"Security by Design"develop
- Regular updates, vulnerability management, conformance assessment
- Reporting of security incidentswithin 24 hours
- Also applies toOpen RAN modules, network software & edge components
- Edge computing in the 5G context
Edge computing enables the processing of sensitive data directly on site - without the public Internet. This is especially forVS-NfD applicationsrelevant if certified hardware and software (BSI-compliant) is used. (Certified hardware and software in accordance withBSI catalog.)
Current state of the art & use in the Bundeswehr
Since approx.2020The implementation of private 5G networks has been established in Germany through frequency allocation and funding programs. The Bundeswehr has been testing its own networks for battlefield communications since 2022 with a focus on resilience and disruption tolerance.
Funding opportunities (Germany & EU)
- BMWK / DLRInnovation projects
- BMDV InnoNT/ 5G Innovation Program
- KfW loansDigital infrastructure
- EU Smart Communities/ Horizon Europe
- CampusOS & Open RAN projects(Fraunhofer et al.)
Funding is possible for:Infrastructure, research, piloting, digitization & security
Conclusion: Opportunities & Responsibility
Private 5G networks offer highSovereigntyandPerformance– but also a high level of responsibility in terms of security, data protection and regulations. Anyone who wants to be a provider or operator should get involved early onNIS2,CRAand familiarize yourself with funding opportunities.
💡 Tip:Anyone planning to operate a 5G network should involve IT security experts, data protection officers and funding consultants at an early stage.
Disclaimer:The information contained in this document on security-related topics, legal requirements and projects - particularly in connection with the Bundeswehr - is based on publicly accessible sources at the time of publication. This is a technically classified presentation and not confidential or security-classified information. No liability is assumed for completeness or legal bindingness. For specific applications, it is recommended to seek legal and safety advice.
Next step: Free initial consultation
Would you like to strategically anchor IT security in your company? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Next step: Free initial consultation
Would you like to strategically anchor IT security in your company? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Related articles
Continue exploring with related insights from our experts.

Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.

Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.

Security Awareness Training: Building Effective Programs and Measuring Impact
The human layer remains the weakest link in cybersecurity. This guide covers how to build an effective security awareness program, run phishing simulations, design role-based training, and measure whether your program actually reduces risk — with benchmarks and KPIs.