SBOM – The new obligation for software security? Increase the security of your supply chain.

Software Bill of Materials (SBOM): The strategic imperative for modern companies
Why SBOMs are essential for your cybersecurity
In a highly networked world, in which a failure of IT operations also results in a failure of business operations for many companies, vulnerabilities in the software used are often the gateway for attackers and the cause of significant portions of operational risks.
Software is complex and has no longer been developed as a monolith for decades, but rather is “assembled” from components and libraries and “supplemented” by the provider's own code. That's where it comes fromSoftware supply chainis very important because often more than 90 percent of the code of a delivered software product does not come from the provider.
The threat of cyberattacks on the software supply chain
Cyber attacks on the software supply chain are an example of how a targeted installation of malware into components or libraries of a widely used software product can cause very high levels of damage.
At least since thenSolarWinds hackWith millions of IT systems affected and more than 18,000 customers who had downloaded the compromised update, everyone knows what the consequences of such an attack can be, not only for the affected provider, but especially for its customers, who are the real target of the attackers.
Attacks on the software supply chain through the installation of malware are not only directed against commercial software, but increasingly also against itOpen source software, especially those used in a critical environment and widely used. A prominent example of this is the one discovered in 2024XZ backdoorin the XZ tools and libraries for Linux. The backdoor, which appears in two releases of the libraries, was discovered about a month after it was "installed", so the damage was limited despite a CVSS score of 10, also because widely used distributions such as Red Hat Enterprise Linux were not affected.
Beyond targeted attacks, there are also widespread vulnerabilities likeLog4Shellthe need to create full transparency about the components and libraries built into software.
Software Bill of Materials: The solution for more transparency
This is exactly where the concept ofSoftware Bill of Materials (SBOM), in German software component list. What was once a niche discussion among experts has become a central topic in application security. The publication of the Federal Office for Information Security (BSI) on the"Shared vision on the topic of Software Bill of Materials (SBOM)"and the associated publication with the title"A Shared Vision of Software Bill of Materials (SBOM) for Cybersecurity"which was created as part of the "Global Government Expert Forum on SBOM" is a further call to everyone who has not yet dealt with it:SBOMs are no longer an option but a strategic necessity.
This article highlights why SBOMs are essential for your company, what role the BSI-backed initiative plays, and how you can overcome the challenges to effectively secure your software supply chain.
What is an SBOM and why is it so crucial?
Imagine you are building a house. You would need a detailed list of all the materials used - from the bricks to the electrical wires to the windows. OneSoftware Bill of Materials (SBOM)is just that for software: a complete, machine-readable list of all the components and libraries included in a software application, with further information about them. This includes relevant licensing information and external APIs. that can be called by the component and the endpoint URIs associated with these APIs and relationships to other code bases. A Software Bill of Materials for a particular software typically includes both open source and commercial software components as well as internal developments.
The four key factors for SBOM relevance
The relevance of SBOMs stems from several key factors:
1. Supply chain transparency
Modern software is almost never monolithic. On average, it consists of hundreds of components, including many from third-party providers. An SBOM creates transparency about which of these components are used, where they come from and which versions are in use.
When everyone along the supply chain has an SBOM for their software, the time to identify and remediate vulnerabilities can be significantly reduced (see Figure 1). Without an SBOM, each actor relies on notification from upstream suppliers to learn that the vulnerability affects their software.
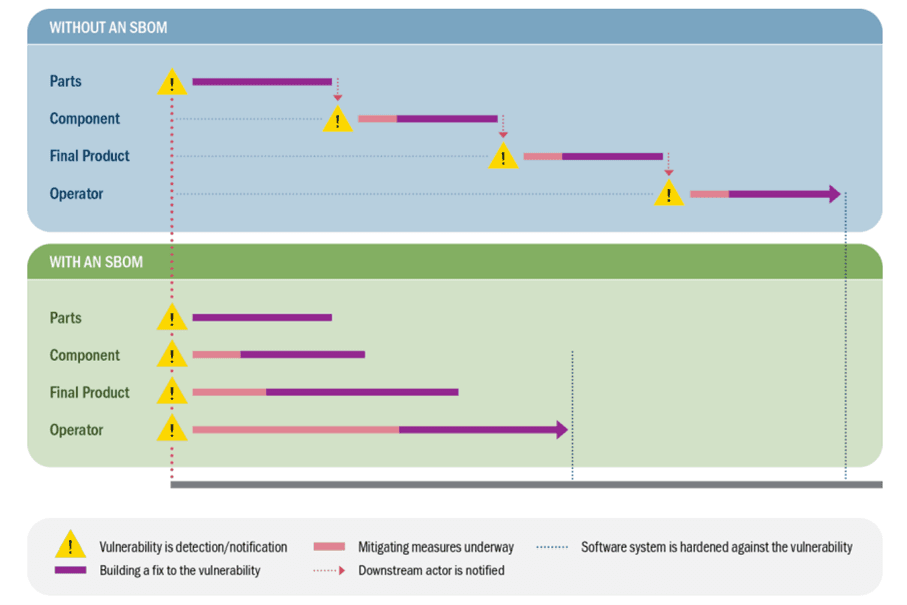
Figure 1. Source:https://www.cisa.gov/sites/default/files/2025-09/joint-guidance-a-shared-vision-of-software-bill-of-materials-for-cybersecurity_508c.pdf
2. Improved vulnerability detection
When a new critical vulnerability in a widely used component or library becomes known, an SBOM enables companies to quickly identify whether and where this component library is used in their software landscape, as illustrated in the following graphic from the "Shared Vision" using the example of the Log4j vulnerability in organizations that have implemented an SBOM. This dramatically speeds up the response to identified vulnerabilities and the treatment of the risks they pose.
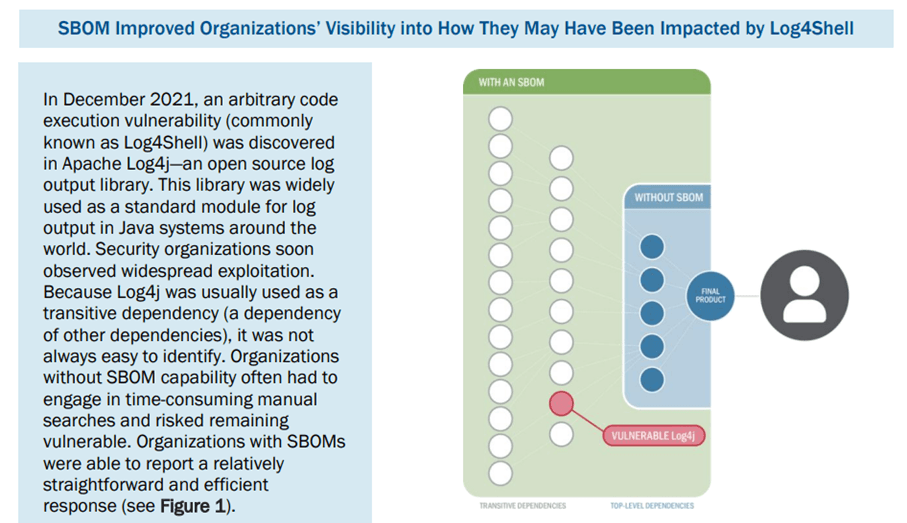
Figure 2. The impact of SBOM on the Log4j vulnerability Source:https://www.cisa.gov/sites/default/files/2025-09/joint-guidance-a-shared-vision-of-software-bill-of-materials-for-cybersecurity_508c.pdf
3. Compliance and Regulation
Governments around the world, and increasingly in Europe, are recognizing the need for SBOMs. In the USA they are through theExecutive Order 14028 The Biden administration has already made it mandatory for software suppliers to the federal government. In Europe, SBOMs are included in the regulation(EU) 2024/2847 (CRA)mandatory.
4. Risk management and license compliance
In addition to security vulnerabilities, SBOMs also help with the detection, management and treatment of license risks and the general risk assessment of software components.
The main advantages of SBOMs
The international guidance “A Shared Vision of Software Bill of Materials (SBOM) for Cybersecurity” lists the following concrete added values:
- Faster response to security vulnerabilities– Example Log4Shell: Anyone who had an SBOM could immediately identify affected systems.
- Better risk management– Transparency across the entire supply chain, including the origin and quality of the software components.
- Optimized software development– Problems with end-of-life components or license conflicts are identified early.
- License Compliance– Risks due to license violations, especially violations of open source licenses, are minimized.
- More trust– Customers, partners and regulators reward companies that take transparency and security seriously.
Who benefits from SBOMs?
Actually all of them:
- Software developer: keep track of dependencies and patch faster.
- Purchasing & procurement: decide on a risk-based basis with a realistic data basis whether software is allowed into the company.
- Operator: immediately recognize where new vulnerabilities strike.
- State cybersecurity authorities & sector-specific regulators: use SBOMs for supervisory tasks within the framework of horizontal and vertical regulation, simplified risk analyzes and joint projects to increase resilience.
SBOM as a building block of “Secure by Design”
The international initiative“Secure by Design”In its second principle, calls for radical transparency and responsibility (“Embrace Radical Transparency and Accountability”). Of course, this also applies to software supply chains. SBOMs are key to putting this principle into practice by:
- automated creation and maintenance throughout the entire software life cycle,
- Integration with security advisories and vulnerability databases,
- Combine with standards such as VEX (Vulnerability Exploitability eXchange) to prioritize risks.
In short: without SBOMs, true software resilience is not possible.
What does this mean for your company?
Regardless of whether it is an SME or a corporation: the time to treat SBOMs as a strategic topic is nownow– even if you do not offer products that fall under the CRA regulation.
The international “Shared Vision” shows clearly: SBOMs are becoming the international de facto standard in software security – especially in Germany, where the BSI has issued the technical guidelines“Technical Guideline BSI TR-03183: Cyber Resilience Requirements for Manufacturers and Products Part 2: Software Bill of Materials (SBOM)"have been pushing forward the topic of SBOM since 2023.
Companies that want to act on this final wake-up call are not only protecting themselves against cyber risk, but also creating oneCompetitive advantage: more trust, shorter response times, better compliance.
Our offer: SBOM advice with real added value
SBOMs are not a buzzword, but a real game changer for cybersecurity.
With the international “Shared Vision” it is clear: future-proof software is transparent – right from the start.
Are you ready to increase transparency in your software supply chain?
As a consulting company for information security, we support you inSBOM strategiesto develop and implement tailored solutions through the implementation of the following activities:
- Analysis of your existing software landscape
- Development of an SBOM strategyfor all relevant company areas
- Integration into your development, operational and security processes
- Training your teamsand support during the introduction
Your goals are our goals: less risk, more transparency, greater resilience.
Contact us for a non-binding initial consultation and find out how you can benefit from our expertise.
Further information can also be found atour website about SBOM CRA.
Next step: Free initial consultation
Would you like to strategically anchor IT security in your company? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Next step: Free initial consultation
📖 Also read:BSI TR-03185-2: Compliance hurdle or strategic lever for your market advantage?
Would you like to strategically anchor IT security in your company? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Related articles
Continue exploring with related insights from our experts.

Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.

Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.

Security Awareness Training: Building Effective Programs and Measuring Impact
The human layer remains the weakest link in cybersecurity. This guide covers how to build an effective security awareness program, run phishing simulations, design role-based training, and measure whether your program actually reduces risk — with benchmarks and KPIs.