TLPT under DORA - Is your company ready for a live cyberattack under regulator supervision?
TheDigital Operational Resilience Act (DORA)has been in use since January 17, 2025 and tightens the regulatory requirements for the digital resilience of financial companies - including ICT risk management, incident reporting, resilience testing, third-party risk management and information exchange. The key point here is to specifically link security monitoring and SIEM capabilities to regulatory control objectives and to develop a risk-based program for themThreat-Led Penetration Testing (TLPT)to build a network that is closely based on the TIBER EU methodology. Anyone who now closes gaps in logging, use case design, supplier transparency or testability not only reduces regulatory risk, but also creates business resilience as a competitive factor.
Why DORA is a top priority for the C Suite
Digital business interruptions have long been a systemic risk for the financial sector. DORA responds to the increasing dependence on ICT services, cloud providers and complex third-party networks. The aim is to enable institutions not only to survive ICT disruptions - including cyber attacks - but also to respond to them in a controlled manner and recover quickly. The regulation applies to around 20 categories of regulated financial companies and explicitly also addresses critical ICT third-party service providers.
The five strategic DORA pillars – management overview
DORA consolidates existing requirements and brings them together in five core areas:
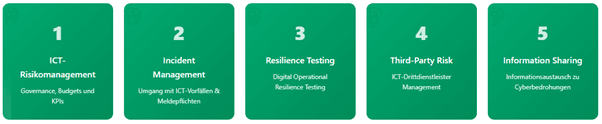
For boards of directors, this means: Governance, budgets and KPIs must be aligned, controlled and made verifiable along these pillars.
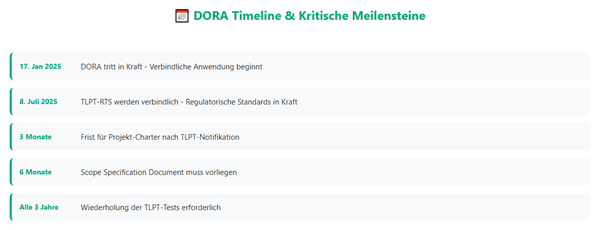
Timeline & Regulatory Pressures
The mandatory applicability of DORA started onJanuary 17, 2025– without generous transition periods. European regulators have repeatedly emphasized that they take a strict enforcement approach; Registers of information on ICT service providers were signaled early on as an immediate supervisory priority. Several national authorities – including BaFin – expect documented implementation schedules and rapid contract revisions with critical ICT providers.
TLPT under DORA: From freestyle to compulsory
Advanced Threat-Informed Penetration Testing (Threat-Led Penetration Testing, TLPT) are mandatory for selected financial companies - determined according to impact, system relevance and risk profile. The European Supervisory Authorities (ESAs), together with the ECB, have developed a Regulatory Technical Standard (RTS) that specifies the methodology, scope, use of internal testers and supervisory cooperation. The RTS reflects the TIBER EU methodology; Financial firms can use national TIBER implementations as long as they are consistent with DORA requirements.
When does my company need to perform TLPT?
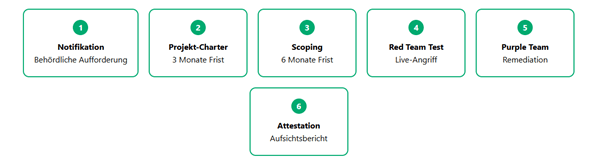
The obligation applies when the responsible TLPT authority addresses your institution according to the criteria anchored in the RTS (including system relevance, risk profile, impact dimensions) and formally requests implementation. There are tight deadlines from notification: initiation information (project plan, control team, communication channels) must be submitted within three months; A detailed scoping of the critical or important functions and associated ICT assets follows within six months.
TLPT & TIBER-EU: Practical convergence
1 | What is Threat-Led Penetration Testing (TLPT)?
Threat-Led Penetration Testing (TLPT) is a regulatory-based red team procedure that describes a framework that replicates the tactics, techniques and procedures of real attackers who are perceived as a real cyber threat. It simulates realistic attacks by state or criminal threat actorscritical and important functions (CIFs)of a financial company to check its cyber resilience under live operating conditions. Unlike classic pen tests, TLPT is strictly based on
- current attacker tactics, techniques and procedures (TTPs),
- coordinated threat modeling (Threat Intel Report) and
- a complete end-to-end attack path with defined “flags” as proof of success. TLPT thus fulfills the requirementArticle 26 DORAto realistically address all three dimensions of the CIA triad (confidentiality, integrity, availability).
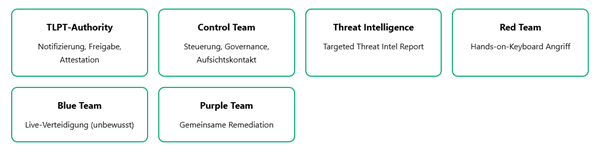
2 | Role model & deliverables
The new oneRTS (EU) 2025/1190defines a more fine-grained role and document set that closely followsTIBER-EU 2025is based on:
3 | Mandatory deliverables and deadlines
4 | What's new in RTS 2025?
- Commitment & reach– TLPT is no longer voluntary (like TIBER), but for institutions that meet the quantitative limits set out in the RTSImpact thresholdsfulfill, obligatory.
- Official notification & fixed timelines(3/6 month milestones) replace self-initiated tests.
- Mutual recognition– Results are recognized EU-wide provided they were carried out in accordance with TIBER-EU or equivalent national framework.
- Purple-Teaming Pflicht– Remediation workshops are now expressly required.
- Internal red teamers permitted– Under strict independence rules, up to two out of three consecutive tests may be filled internally.
- Multi-party & supply chain testing– enable group or sector-wide attacks to cover shared services (e.g. cloud).
- Scenario X– optional “forward-looking” attack for emerging TTPs.
5 | Challenges from practice
- Resources & Costs– Full tests last 9-12 months, bind Blue, Red, Purple and Control teams and must be repeated every three years at the latest.
- Data protection & confidentiality– Live attacks on production environments require strict logging, forensics and leak prevention measures.
- Supplier dependencies– Integration of critical third-party/cloud providers increases complexity (legal agreements, access, liability).
- Market capacities– A few qualified providers (TIPs/RTTs) meet the minimum references required in the RTS.
- Supervisory coordination– For cross-border institutions, several TLPT authorities must act together; the RTS outlines cooperation mechanisms for this.
6 | Synergies: TIBER-EU as a “Fast Track”
TheTIBER-EU revision 2025The content was mirrored on the RTS. Anyone who already uses TIBER-EU automatically meets the TLPT method requirements, including new terminology (CIFs, CT, RTT) and mandatory Purple Team remediation. This means that the test overhead is significantly reduced for multinational institutes: a single TIBER test, properly coordinated with the authority pool, replaces several country-specific TLPTs.
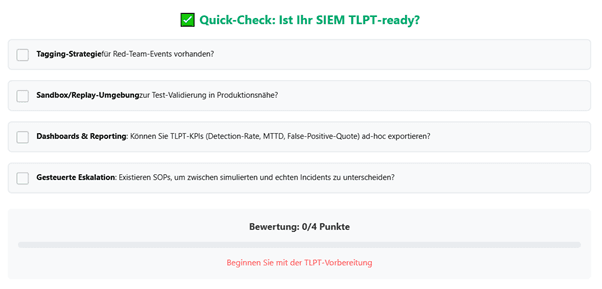
SIEM as a DORA enabler and TLPT catalyst
The Digital Operational Resilience Act (DORA) not only requires continuous monitoring of ICT risks, but also a three-year cycle from 2025Threat‑Led Penetration Testing (TLPT). A SIEM is the connecting nervous system - it makes TLPT measurable, controllable and detectable.
Why does SIEM belong to TLPT?
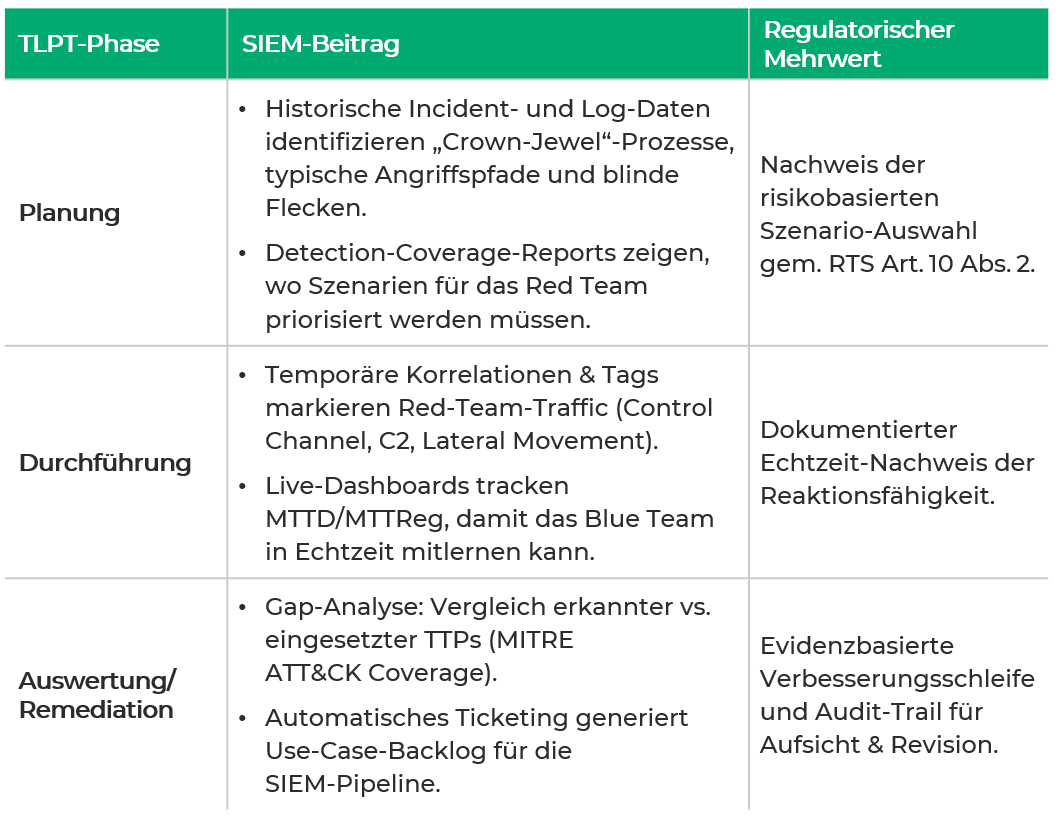
Advanced SIEM UseCase categories for DORA and TLPT
- Criticality-based asset & service correlation:Mapping of logs to DORA-critical functionsandTLPT scenario scopes.
- Incident classification & thresholds:Refined thresholds to differentiate TLPT events from real incidents.
- MTTD/MTTReg real-time metrics:Live display during TLPT to reinforce learning.
- Third-party/supply chain monitoring:Integration of red team impacts on outsourced services.
- MITER ATT&CK use case library:Willingness to cover TLPT‑TTPs without signature adjustment.
- Business continuity triggers:Validate that TLPT-induced failover is detected as planned.
- Data integrity & backup monitoring:Verifying recovery from simulated ransomware attacks.
- Threat intelligence feeds:Enrichment of TLPT findings for sustainable detection use cases.
These categories shouldrisk basedprioritized, provided with clear control objectives and in oneSIEM and TLPT backlogbe anchored. This creates a closed feedback loop: TLPT delivers realistic attack patterns - the SIEM translates them into permanent use cases and metrics. This transforms the SIEM from a passive log archive into an active resilience engine that continuously demonstrates DORA conformity.
Governance: roles, responsibilities & reporting to the board
A resilient oneThreat-Led Penetration Testing-The DORA / TIBER-EU program only works if the responsibilities are clearly distributed:
- CISOretains overall responsibility and appoints oneTLPT owneras an operational hub between red team lead, blue team / SOC, threat intelligence andCRO.
- CROevaluates the risks derived from the tests, prioritizes findings in the ORSA process and monitors implementation.
- CIOprovides isolated test environments as well as “white-listed” production access and coordinates change-freeze windows.
- Legal Department & Procurementanchor contractual cooperation and “controlled live-fire” clauses for all third-party providers involved (cloud, MSSP, etc.) - including exit and sub-outsourcing rules.
- Business Managersapprove test scope and accept residual risks.
Reporting lines:
All key points - scoping approval, go/no-go decision, 24-hour notification of critical findings and final results - must be prepared as board templates (heat map of the attack paths, maturity score, cost/benefit analysis). The results are mandatory in the annual ICT risk profile, the information register and the SIEM roadmap.
Current status of TLPT-RTS & important deadlines
The delegated regulation with the RTS on TLPT was published in the Official Journal of the EU and entered into force onJuly 8, 2025in force. This stipulates the requirements of Article 26 DORA in a binding manner - including criteria for identifying institutions subject to TLPT, scope definition, methodology, use of internal testers and supervisory cooperation rules. Institutes should reflect their test programs against these standards in a timely manner.
Roadmap: 6-step action agenda for the next 12 months
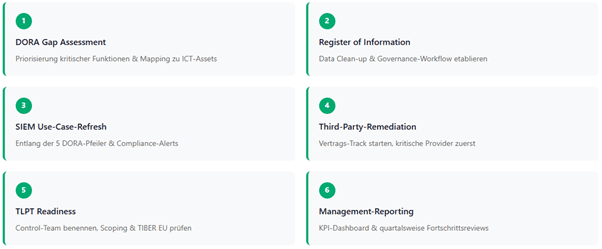
Conclusion
DORA is not just a compliance project – it is a catalyst for integrated cyber, operational and supply chain resilience. Anyone who holistically integrates security monitoring, contract management, business continuity and threat-oriented testing reduces regulatory risks, strengthens customer trust and creates the basis for scalable growth in a highly digitalized financial world.
Next step: Free initial consultation
Would you like to implement DORA compliance in a timely manner? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Next step: Free initial consultation
Would you like to implement DORA compliance in a timely manner? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Next step: Free initial consultation
📖 Also read:BaFin update on AI & DORA
📖 Also read:BaFin update on AI & DORA
Would you like to implement DORA compliance in a timely manner? Our experts will be happy to advise you - without obligation and in a practical manner.Arrange an initial consultation now →
Related articles
Continue exploring with related insights from our experts.

Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.

Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.

Security Awareness Training: Building Effective Programs and Measuring Impact
The human layer remains the weakest link in cybersecurity. This guide covers how to build an effective security awareness program, run phishing simulations, design role-based training, and measure whether your program actually reduces risk — with benchmarks and KPIs.