What Is IAM? Identity and Access Management — The Complete Guide
Identity and Access Management (IAM) is the framework of policies, processes, and technologies that manages digital identities and controls who can access what within an organization. In a world where the network perimeter has dissolved — with cloud adoption, remote work, and SaaS proliferation — identity has become the primary security boundary. Over 80% of data breaches involve compromised credentials, making IAM not an IT convenience but a security imperative.
This guide explains what IAM is, how it works, the core components every organization needs, how IAM relates to compliance requirements like DORA, NIS2, and GDPR, and how to implement IAM in practice. Whether you are building IAM from scratch or modernizing a legacy system, this is the practical reference.
What Is Identity and Access Management?
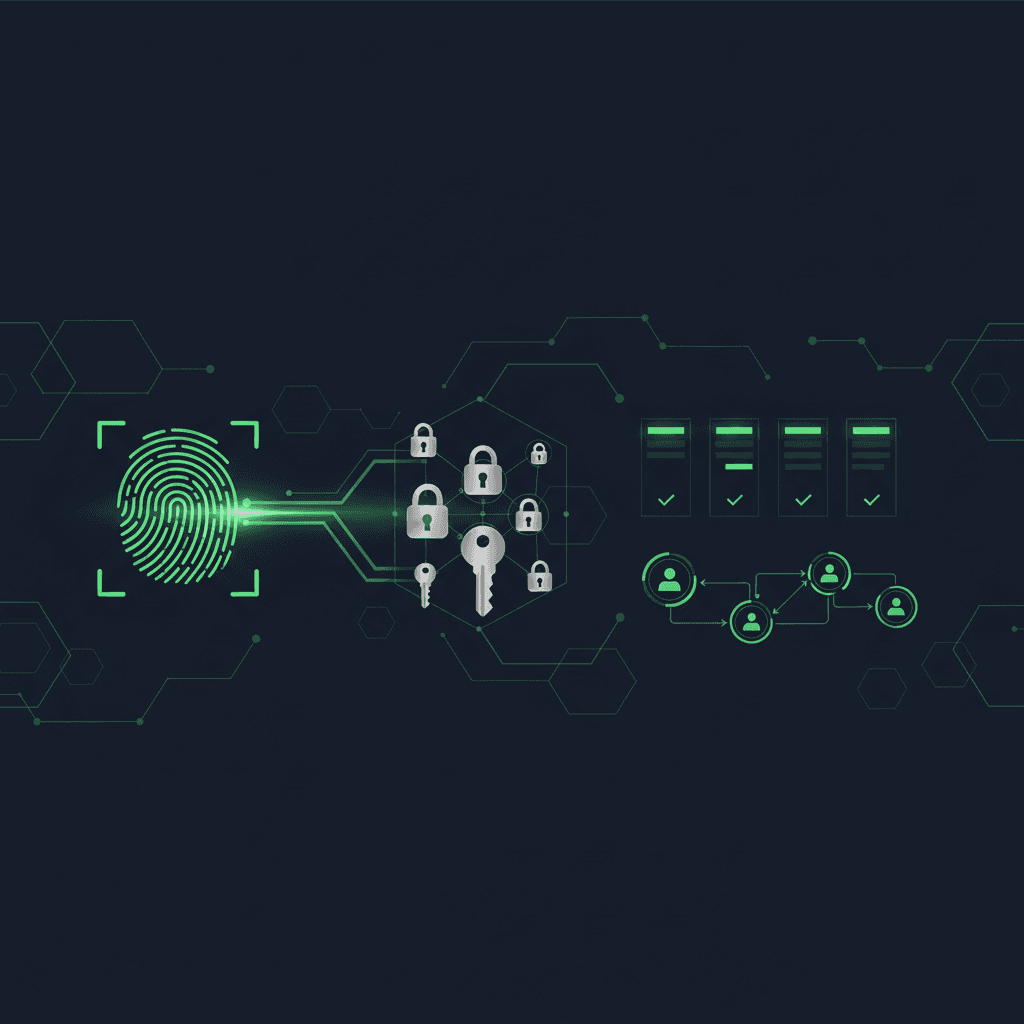
IAM encompasses every process and technology involved in managing digital identities and controlling access to organizational resources. It answers three fundamental questions: Who are you? (Authentication) What are you allowed to do? (Authorization) What did you do? (Auditing). An effective IAM system ensures that the right people have the right access to the right resources at the right time — and that nobody else does.
Core Components of IAM
Identity Lifecycle Management
Managing identities from creation through modification to deactivation covers the complete lifecycle: Provisioning (creating accounts, assigning initial roles during onboarding), Modification (adjusting access when roles change, projects start or end, or organizational changes occur), Deprovisioning (revoking all access promptly when someone leaves the organization or changes roles). Automation is critical here. Manual provisioning creates delays during onboarding and, more dangerously, orphaned accounts and lingering access rights after departure. Studies show that 40% of organizations take more than a week to deprovision former employees — each day representing a potential security exposure.
Authentication: Verifying Identity
Authentication verifies that users are who they claim to be. Modern authentication has evolved well beyond passwords:
- Passwords: The baseline, but increasingly insufficient alone. 81% of breaches involve weak or stolen passwords.
- Multi-Factor Authentication (MFA): Combines something you know (password) with something you have (phone, hardware key) and/or something you are (biometrics). MFA blocks 99.9% of automated credential attacks.
- Passwordless Authentication: FIDO2/WebAuthn standards enable login without passwords entirely, using hardware security keys or platform authenticators (fingerprint, face ID). More secure and better user experience.
- Adaptive/Risk-Based Authentication: Adjusts authentication requirements based on context — device health, location, behavior patterns, time of access. Low-risk logins proceed smoothly; anomalous access triggers step-up verification.
Authorization: Controlling Access
Once identity is verified, authorization determines what the user can do. Three primary models:
- Role-Based Access Control (RBAC): Access determined by job role. Simple to implement and manage. Works well for organizations with clear role definitions. The most common model.
- Attribute-Based Access Control (ABAC): Access determined by user attributes (department, clearance level), resource attributes (sensitivity, owner), and context (time, location, device). More granular than RBAC but more complex to manage.
- Policy-Based Access Control (PBAC): Access determined by organizational policies expressed as rules. Combines the structure of RBAC with the flexibility of ABAC. Increasingly used in cloud environments.
Most organizations use RBAC as a foundation and layer ABAC for fine-grained control where needed.
Single Sign-On (SSO)
SSO allows users to authenticate once and access multiple applications without re-entering credentials. This reduces password fatigue, eliminates credential reuse across services, and provides a single point for MFA enforcement. Modern SSO uses protocols like SAML 2.0 and OpenID Connect. Combined with MFA, SSO actually improves security while reducing friction — a rare win-win in security.
Privileged Access Management (PAM)
PAM provides enhanced controls for administrative accounts — the keys to the kingdom. Core capabilities: just-in-time access (privileges elevated only when needed, for a limited time), credential vaulting (admin passwords stored in an encrypted vault, rotated automatically), session recording (full audit trail of privileged actions), and break-glass procedures (emergency access with mandatory post-use review). Compromised admin accounts are the #1 path to complete environment compromise. PAM is non-negotiable for any serious security program.
Identity Governance and Administration (IGA)
IGA provides the oversight layer: regular access reviews (certifications), segregation of duties (SoD) enforcement, compliance reporting, and policy management. Access reviews ensure that accumulated permissions are periodically validated — particularly important for users who change roles internally. IGA platforms automate these reviews, flagging anomalous access and generating audit-ready reports.
IAM and Zero Trust
Zero Trust architecture makes identity the core security control. Instead of trusting anything inside the network perimeter, Zero Trust requires explicit verification for every access request — regardless of location. IAM provides the foundation: strong authentication verifies identity, continuous authorization checks validate every access request, device trust ensures endpoints meet security baselines, and behavioral analytics detect anomalous patterns. Without robust IAM, Zero Trust is impossible. IAM is not a component of Zero Trust — it is the prerequisite.
IAM for Compliance
IAM is central to nearly every regulatory framework:
- DORA (Articles 9-10): Requires ICT access management controls including strong authentication, least-privilege access, and regular access reviews for financial institutions.
- NIS2 (Article 21): Mandates access control and identity management as core cybersecurity risk management measures.
- GDPR (Article 32): Access controls are a fundamental technical measure. Regular access reviews demonstrate accountability. Right of access requires knowing what data each identity can reach.
- ISO 27001 (Annex A 5.15–5.18, 8.2–8.5): Comprehensive identity and access management controls covering access policy, user registration, privilege management, and authentication.
- SOC 2 (CC6.1–CC6.3): Logical and physical access controls, user provisioning, and authentication are core Trust Services Criteria.
Implementing IAM: A Practical Roadmap
- Month 1–2: Foundation — Deploy centralized identity directory (Azure AD/Entra ID, Okta, or equivalent). Enforce MFA for all users across all applications. Implement SSO for critical business applications.
- Month 2–4: Role Model — Define RBAC role model based on job functions. Start with broad roles and refine over time. Conduct initial access review to clean up existing permissions.
- Month 4–6: Automation — Automate provisioning and deprovisioning (connect IAM to HR system for joiners/movers/leavers). Implement self-service password reset. Deploy PAM for administrator accounts.
- Month 6–12: Maturity — Implement IGA for regular access certifications. Add adaptive authentication for risk-based access decisions. Extend IAM to cloud platforms and SaaS applications. Establish ongoing access review cycle (quarterly for privileged, semi-annual for standard).
IAM Architecture: Cloud vs. On-Premises
Cloud IAM (IDaaS — Identity as a Service) has become the default for most organizations. Platforms like Microsoft Entra ID, Okta, and Ping Identity provide: faster deployment, automatic updates, built-in MFA and SSO, API-based integration with SaaS applications, and elastic scalability. On-premises IAM (Active Directory, LDAP) remains relevant for organizations with strict data residency requirements or legacy applications that cannot integrate with cloud identity providers. Most enterprises adopt a hybrid model: cloud IAM for modern applications and user access, with directory synchronization to on-premises systems for legacy compatibility.
Common IAM Mistakes
- Over-provisioning: Granting more access than needed because it is easier than determining exact requirements. This violates least privilege and expands the blast radius of any compromise.
- No deprovisioning process: Former employees retaining access for weeks or months after departure. Automate deprovisioning through HR system integration.
- Ignoring service accounts: Non-human identities (API keys, service accounts, machine credentials) often have excessive privileges and no expiration. Include them in IAM governance.
- MFA fatigue attacks: Repeatedly sending MFA push notifications until the user approves. Counter with number matching, phishing-resistant MFA (FIDO2), and anomaly detection.
- No access reviews: Permissions accumulate over time as users change roles. Regular access certification catches drift before it becomes a vulnerability.
Frequently Asked Questions
What is the difference between IAM and PAM?
IAM manages all user identities and their standard access rights. PAM is a specialized subset that provides enhanced controls specifically for privileged accounts (administrators, root accounts, service accounts). Think of IAM as the access management system for everyone, and PAM as the high-security vault for the most powerful credentials. Every organization needs IAM; organizations with administrative accounts (which is everyone) also need PAM.
Is SSO a security risk?
SSO reduces the number of credentials users manage, which means fewer passwords to forget, reuse, or have phished. Combined with MFA, SSO improves security compared to managing separate credentials for each application. The risk is that a compromised SSO credential grants broad access — which is why MFA on the identity provider is absolutely non-negotiable. The security gain from eliminating password reuse across applications outweighs the concentration risk, provided MFA is enforced.
How do we implement IAM in a mid-sized company?
Start with: centralized identity directory (Entra ID or Okta), universal MFA, SSO for critical applications, a basic RBAC role model, and automated onboarding/offboarding tied to the HR system. This foundation covers 80% of IAM value and can be implemented in 3–6 months with a budget of EUR 20,000–50,000 for mid-market solutions. Expand from there to PAM, IGA, and adaptive authentication as maturity grows.
What does IAM cost?
Cloud IAM platform licensing: EUR 3–12 per user per month depending on features. For a 500-person organization: EUR 18,000–72,000/year. PAM: EUR 20,000–80,000/year for mid-market solutions. Implementation: EUR 30,000–100,000 depending on complexity. The ROI is demonstrated through reduced help desk costs (30–40% of tickets are password-related), faster onboarding, regulatory compliance evidence, and breach prevention.
How does IAM relate to Zero Trust?
IAM is the foundation of Zero Trust architecture. Zero Trust requires explicit verification of every access request, and IAM provides the mechanisms: strong authentication (who is requesting?), continuous authorization (should they have access given the current context?), and device trust assessment (is their device secure?). You cannot implement Zero Trust without mature IAM. Start with IAM fundamentals, then build Zero Trust capabilities on top.