IT Budget 2027: How to Prioritize Cybersecurity Investments for Maximum Impact
Budget season for 2027 arrives against a backdrop of active DORA enforcement, NIS2 penalties being levied, AI Act compliance deadlines, rising ransomware costs, and persistent economic pressure to demonstrate ROI on every security euro spent. CISOs face the perennial challenge: protect more with roughly the same budget. The organizations that allocate well will be measurably more secure; those that spread budget thinly across every possible initiative will achieve mediocrity everywhere.
This guide provides a framework for prioritizing cybersecurity investments by impact, with spending benchmarks, ROI considerations for each investment category, and practical advice for justifying security budget to the board.
Cybersecurity Spending Benchmarks
Average cybersecurity spending as a percentage of IT budget by sector: Financial services: 12–15%. Healthcare: 8–12%. Manufacturing: 6–10%. Professional services: 8–12%. Retail and e-commerce: 5–8%. If your cybersecurity spending is significantly below these benchmarks, you are accumulating risk debt that compounds over time. However, spending more than the benchmark does not automatically mean better security — allocation matters more than total spend.
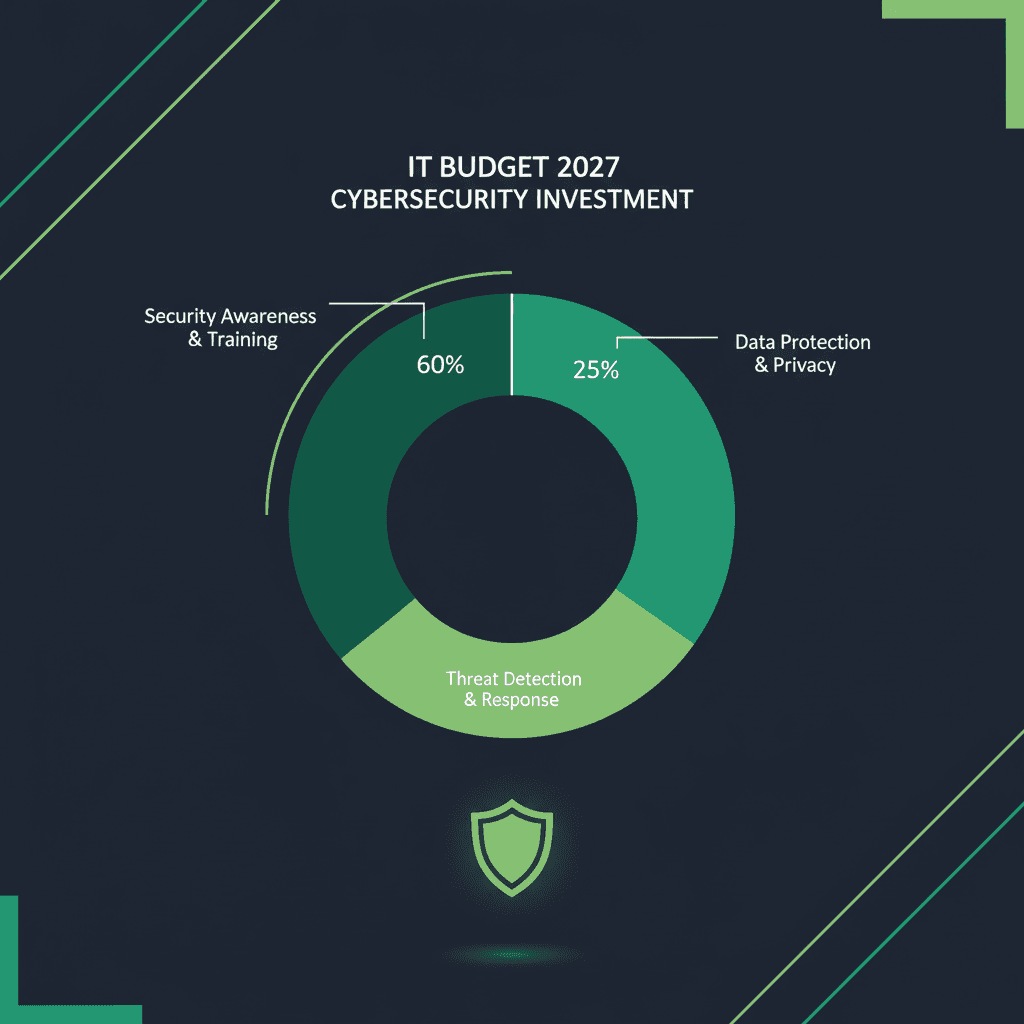
Top 5 Investment Priorities for 2027
1. Identity and Access Management (Highest Priority)
Over 80% of breaches involve compromised credentials. Identity is the new perimeter, and IAM investment has the highest per-euro security impact. Budget priorities: universal MFA enforcement (if not already complete), privileged access management (PAM) for admin accounts, identity governance for regular access reviews, and conditional access policies with risk-based authentication. Recommended allocation: 15–20% of security budget. Expected ROI: 30–40% reduction in credential-based incidents, 40–60% reduction in access-related audit findings.
2. Detection and Response
You cannot prevent every intrusion — speed of detection and response determines impact. Budget priorities: XDR or managed detection and response (MDR) for 24/7 monitoring, incident response retainer with a specialized firm, automated response playbooks for common scenarios, and threat intelligence feeds relevant to your industry. Recommended allocation: 20–25% of security budget. Expected ROI: 60–70% reduction in mean time to detect (MTTD), measurable reduction in breach impact.
3. Cloud Security
Cloud environments expand, and misconfigurations remain the #1 cause of cloud breaches. Budget priorities: CSPM (Cloud Security Posture Management) for continuous configuration monitoring, cloud-native WAF, workload protection, and secure DevOps tooling for CI/CD pipelines. Recommended allocation: 10–15% of security budget.
4. Compliance Automation
DORA, NIS2, AI Act — the compliance burden grows while manual compliance does not scale. Budget priorities: GRC platform for multi-framework compliance management, automated evidence collection, policy-as-code for infrastructure compliance, and continuous compliance monitoring. Recommended allocation: 8–12% of security budget. Expected ROI: 50–70% reduction in compliance audit preparation time.
5. Security Awareness and Training
The human layer requires consistent investment, not one-off spending. Budget priorities: security awareness platform with monthly phishing simulations, role-based training (developers, finance, executives), tabletop exercises for incident response, and security champion program. Recommended allocation: 3–5% of security budget.
Justifying Security Budget to the Board
Frame security investment in business terms:
- Risk reduction: Quantify risk in EUR using incident probability and estimated impact. A EUR 200K/year investment preventing a EUR 2M ransomware incident is a 10:1 return.
- Regulatory penalty avoidance: NIS2 fines up to EUR 10M, DORA enforcement actions, AI Act penalties up to EUR 35M. Compliance investment is insurance against these outcomes.
- Insurance premium reduction: Demonstrated security controls (MFA, EDR, ISO 27001) reduce cyber insurance premiums by 15–40%.
- Competitive advantage: Security certifications (ISO 27001, SOC 2) are increasingly procurement requirements. Security investment enables revenue.
Frequently Asked Questions
What percentage of IT budget should go to cybersecurity?
Industry average is 10–14% of IT budget. Regulated industries (finance, healthcare) should target 12–15%. The absolute number matters less than whether you are addressing your actual risk profile. A risk-based approach may justify spending more or less than the average.
Should we build or buy security capabilities?
For most mid-sized organizations: buy. Managed security services (MDR, managed SIEM) provide 24/7 coverage at a fraction of in-house SOC costs. Build only where you have unique requirements or where the capability is a competitive differentiator. The build vs. buy decision should be revisited annually as the organization grows.
How do we measure security ROI?
Track: incident frequency and severity trends, mean time to detect and respond, compliance audit findings (should decrease), insurance premium changes, and security-related procurement wins/losses. Combine quantitative metrics with qualitative risk reduction narrative. Perfect ROI measurement for security is impossible — but directional measurement is achievable and valuable.