CRA December 2027: Full Compliance Deadline — The 12-Month Countdown for Manufacturers
December 11, 2027 is the hard deadline for full Cyber Resilience Act compliance. After this date, products with digital elements that do not meet essential cybersecurity requirements, carry CE marking, and have completed conformity assessment cannot legally be placed on the EU market. Market surveillance authorities can order recalls, impose fines up to EUR 15 million, and issue public warnings. There is no extension and no grandfathering for non-compliant products.
For manufacturers who have not yet completed preparation, this guide provides a month-by-month roadmap for the final 12 months. Every month counts — late action means either non-compliance or market withdrawal.
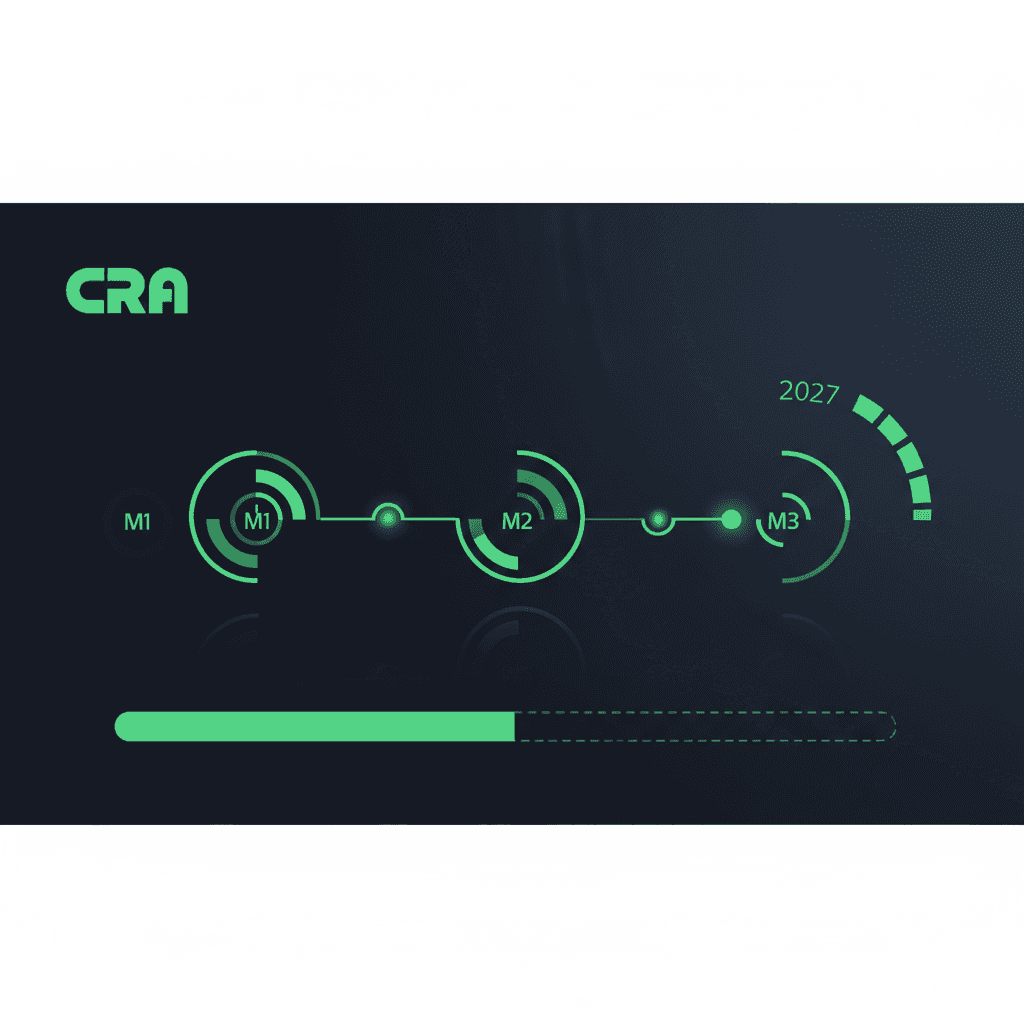
CRA Timeline Recap
- December 10, 2024: CRA entered into force
- September 11, 2026: Vulnerability reporting obligation active (already past)
- December 11, 2027: Full compliance deadline for all essential requirements
- Ongoing: 5-year minimum security update obligation from market placement
12-Month Roadmap
Months 1–3: Inventory and Classification
Complete a full inventory of all products with digital elements that you place on the EU market. For each product: confirm CRA applicability (is it a product with digital elements with a network connection?), classify by risk tier (default, Class I, Class II, or critical per Annex III/IV), identify the conformity assessment path (self-assessment vs. third-party), and catalog all software components (begin SBOM generation if not started).
Months 3–6: Security-by-Design Implementation
Address gaps against CRA essential requirements (Annex I Part I): ensure secure default configurations (no default passwords, unnecessary ports disabled), implement or verify automatic security update capability with user opt-out, verify encryption for data at rest and in transit where applicable, review access control mechanisms, assess and reduce attack surface (disable unnecessary features and services), and verify data minimization (process only data necessary for intended purpose). For most products, this is the most effort-intensive phase. Prioritize products with the highest regulatory exposure (Class II, high-volume products).
Months 6–9: SBOM and Vulnerability Handling
Generate complete SBOMs for all products in CycloneDX or SPDX format. Establish or formalize the vulnerability handling process (if not already done for September 2026 reporting). Publish the Coordinated Vulnerability Disclosure (CVD) policy. Set up continuous vulnerability monitoring for all product components. Test the ENISA reporting workflow end-to-end.
Months 9–12: Conformity Assessment and CE Marking
For default and Class I products with harmonized standards: complete internal conformity assessment, documenting compliance against each essential requirement. For Class II products: engage a notified body for third-party assessment (allow 2–3 months for the assessment process). Prepare technical documentation per Annex VII. Draft the EU declaration of conformity. Affix CE marking to compliant products. Train sales, distribution, and customer-facing teams on CRA requirements and customer inquiries. Retain all documentation for 10 years.
What Full Compliance Requires
Essential Security Requirements (Annex I Part I)
- No known exploitable vulnerabilities at time of market placement
- Secure by default configuration
- Data protection (confidentiality, integrity, availability)
- Access control and authentication
- Minimal attack surface
- Automatic security update capability
- Resilience against denial-of-service
Vulnerability Handling (Annex I Part II)
- Documented vulnerability handling process
- Coordinated vulnerability disclosure policy (public)
- SBOM for each product
- Timely, free security patches
- 5-year minimum security support
Conformity Assessment
- Internal assessment (default and Class I with standards) or third-party assessment (Class II and Class I without standards)
- Technical documentation per Annex VII
- EU declaration of conformity
- CE marking affixed to product
Frequently Asked Questions
What happens if we miss the deadline?
Products that do not comply cannot legally be placed on the EU market. Market surveillance authorities can order recalls, market withdrawals, and impose fines up to EUR 15 million or 2.5% of global turnover. The reputational damage from a public product recall can exceed the financial penalty. Products already on the market must also be brought into compliance.
Does the CRA apply to SaaS products?
Pure SaaS without client-side components is generally excluded. But if your SaaS includes any downloadable software (desktop client, mobile app, browser extension), those components are in scope. Review your product architecture carefully.
Can we sell non-compliant products after December 2027?
No. There is no grandfathering provision. Products already on the market before the deadline must also meet CRA requirements. Non-compliant products must be withdrawn. The 5-year security support obligation applies from the date of market placement, not from the compliance deadline.