Third-Party Risk Management: The Complete TPRM Guide for 2026

Third-party risk management (TPRM) is the discipline of identifying, assessing, and mitigating risks that arise from business relationships with external parties — vendors, suppliers, cloud providers, outsourcing partners, and service providers. With supply chain attacks rising dramatically and regulations like DORA and NIS2 mandating vendor risk management, TPRM has moved from procurement checkbox to board-level strategic priority.
This guide covers the full TPRM lifecycle: vendor identification and classification, due diligence and assessment, contract management, continuous monitoring, DORA-specific requirements, and practical tools for organizations at every maturity level.
Why TPRM Matters Now
Three forces drive TPRM urgency: Supply chain attacks (SolarWinds, MOVEit, Log4j, 3CX) demonstrated that attackers target the weakest link in the chain. High-profile breaches through third parties now account for approximately 15% of all data breaches, and the percentage is growing. Regulation has caught up — DORA Articles 28–30 mandate comprehensive ICT third-party risk management for financial institutions. NIS2 Article 21 requires supply chain security as a core cybersecurity measure. Cloud adoption means critical business functions increasingly depend on external providers whose security posture you do not directly control.
The TPRM Lifecycle
1. Vendor Identification and Inventory
The foundation of TPRM is knowing who your third parties are. Maintain a complete, current inventory of all vendors, suppliers, and service providers. For each, document: what service or product they provide, what data they access or process, which business functions depend on them, contract terms and SLAs, and primary contact and escalation paths. Many organizations discover during their first TPRM inventory that they have 2–3x more third-party relationships than leadership estimated — shadow IT, departmental SaaS subscriptions, and inherited vendor relationships are common sources of hidden risk.
2. Risk Classification
Not all vendors carry equal risk. Classify each by:
- Tier 1 (Critical): Vendor failure would directly disrupt critical business functions, or vendor processes sensitive/regulated data. Full due diligence, continuous monitoring, and regular audits. Typically 10–20% of vendors.
- Tier 2 (Important): Vendor provides significant but replaceable services, or processes internal data. Standard due diligence, periodic reviews. Typically 20–30% of vendors.
- Tier 3 (Standard): Low-risk vendors with minimal data access and easily replaceable services. Lightweight assessment, automated monitoring. Typically 50–70% of vendors.
Focus governance effort on Tier 1 vendors — that is where the concentration risk and regulatory exposure lie.
3. Due Diligence and Assessment
Before onboarding and periodically thereafter, assess vendor security posture:
- Security questionnaires: SIG (Shared Assessments), CAIQ (Cloud Security Alliance), or custom questionnaires aligned with your risk framework.
- Independent certifications: ISO 27001 certificate, SOC 2 Type II report, BSI C5 attestation, PCI DSS compliance.
- Penetration test results: Request recent external pentest reports or vulnerability assessment summaries.
- Financial stability: Dun & Bradstreet or equivalent financial health check — a vendor that goes bankrupt creates operational risk.
- Regulatory compliance: Confirm the vendor meets applicable regulatory requirements (GDPR, DORA, NIS2).
For critical vendors under DORA, assessment must specifically cover ICT risk management capabilities, incident reporting capacity, and business continuity provisions.
4. Contract and SLA Management
Encode risk management requirements in contracts:
- Security standards and audit rights: The right to audit the vendor’s security controls, either directly or through independent assessment.
- Incident notification timelines: Align with regulatory requirements (DORA staggered incident notifications (initial within 4h of classification and ≤24h of awareness, intermediate within 72h, final within 1 month), NIS2 24h/72h).
- Data processing agreements: GDPR Article 28 compliant, with clear data handling, retention, and deletion provisions.
- Business continuity and DR commitments: Documented recovery capabilities, tested continuity plans, defined RTOs.
- Exit strategy provisions: Data extraction procedures, transition timelines, and cooperation obligations during vendor transitions.
- Subcontracting limits: Control over further subcontracting of services, especially for data processing and critical ICT functions.
5. Continuous Monitoring
Annual assessments are insufficient for critical vendors. Implement continuous monitoring:
- Security rating services: External security posture scoring based on observable indicators — patching cadence, exposed services, email security, malware activity.
- Vulnerability intelligence: Automated alerts when vulnerabilities affecting vendor products are published.
- Financial health monitoring: Credit rating changes, legal proceedings, and ownership changes that could affect service continuity.
- Dark web monitoring: Detection of vendor data, credentials, or intellectual property on underground forums.
6. Incident Response and Exit Management
When a vendor experiences a security incident: activate the vendor incident response process, conduct joint impact assessment, coordinate containment and remediation, document timeline and actions for regulatory reporting, and conduct post-incident review of the vendor relationship. Exit planning should begin before it is needed — document data extraction procedures, identify alternative vendors for critical services, and define contractual obligations during and after transition.
DORA Third-Party Risk Management (Articles 28–30)
DORA imposes the most detailed third-party risk management requirements of any EU regulation:
- ICT third-party register: Maintain a complete register of all ICT service providers, including service descriptions, criticality classification, and contract details. This register must be available to competent authorities on request.
- Pre-contractual assessment: Before engaging ICT providers, assess their ICT risk management capabilities, business continuity provisions, and regulatory compliance status.
- Mandatory contract clauses: DORA Article 30 specifies minimum contract requirements including performance targets, incident notification obligations, audit rights, exit strategy, and data location provisions.
- Concentration risk: Assess and mitigate concentration risk from over-reliance on single providers or a small number of providers for critical ICT functions.
- Critical ICT provider oversight: The ESAs maintain an oversight framework for ICT providers designated as critical at the EU level. Financial institutions using these providers face additional monitoring and reporting requirements.
Frequently Asked Questions
How many vendors should we assess in detail?
Focus full due diligence on Tier 1 vendors (critical business function or sensitive data access) — typically 10–20% of your vendor portfolio. Use standardized questionnaires for Tier 2 and automated monitoring for Tier 3. The effort should be proportional to the risk, not applied uniformly across all vendors.
What does DORA require for ICT third-party management?
DORA Articles 28–30 require: a register of all ICT third-party providers, risk assessment before contracting, mandatory contract clauses (audit rights, exit strategy, subcontracting limits), monitoring of critical ICT providers, and exit strategies. The ESAs maintain an EU-level oversight framework for providers designated as critical.
How do we handle vendor security incidents?
Establish a vendor incident response process: immediate notification requirement (contractual), joint impact assessment with the vendor, coordinated containment and remediation, root cause analysis, and post-incident review of the vendor relationship. Align notification timelines with regulatory reporting requirements (DORA, NIS2, GDPR).
What tools support TPRM?
Security rating platforms for continuous external monitoring. GRC platforms for vendor assessment workflow. Questionnaire platforms for due diligence management. Most mid-sized organizations can start with structured spreadsheets and graduate to dedicated tools as the program matures.
How often should vendors be reassessed?
Tier 1 (critical): annually with continuous monitoring. Tier 2 (important): every 2 years with periodic monitoring. Tier 3 (standard): at onboarding and upon significant change. Additionally: reassess whenever a vendor experiences a security incident, ownership change, or significant service modification.
Related articles
Continue exploring with related insights from our experts.
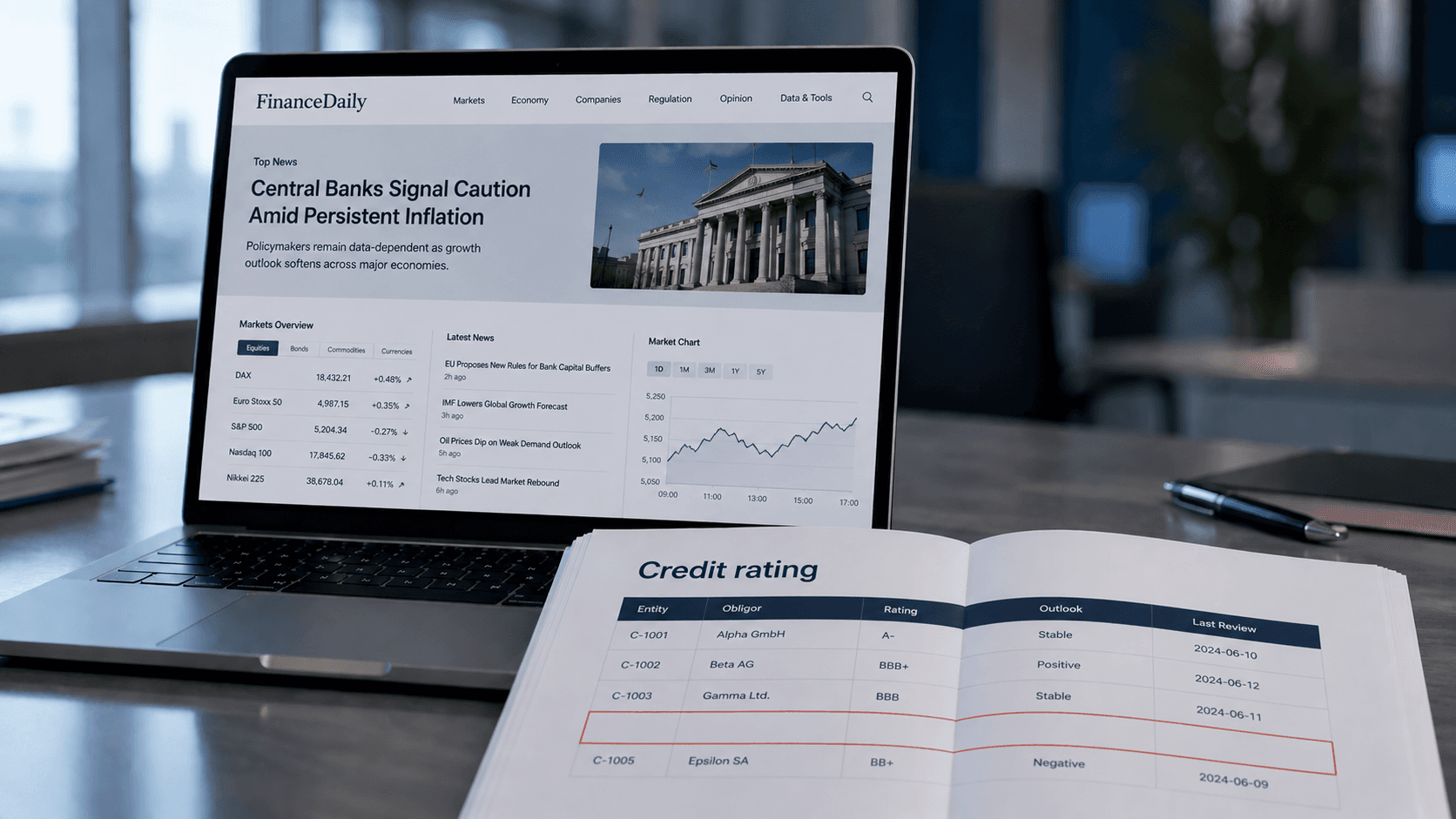
Credit Risk Modeling Trends 2026: Five Shifts Risk Managers Should Prepare For
The credit risk function of 2026 looks materially different from the one most banks still operate. Here are the five shifts, from generative AI to ESG integration, that risk managers should plan for now.
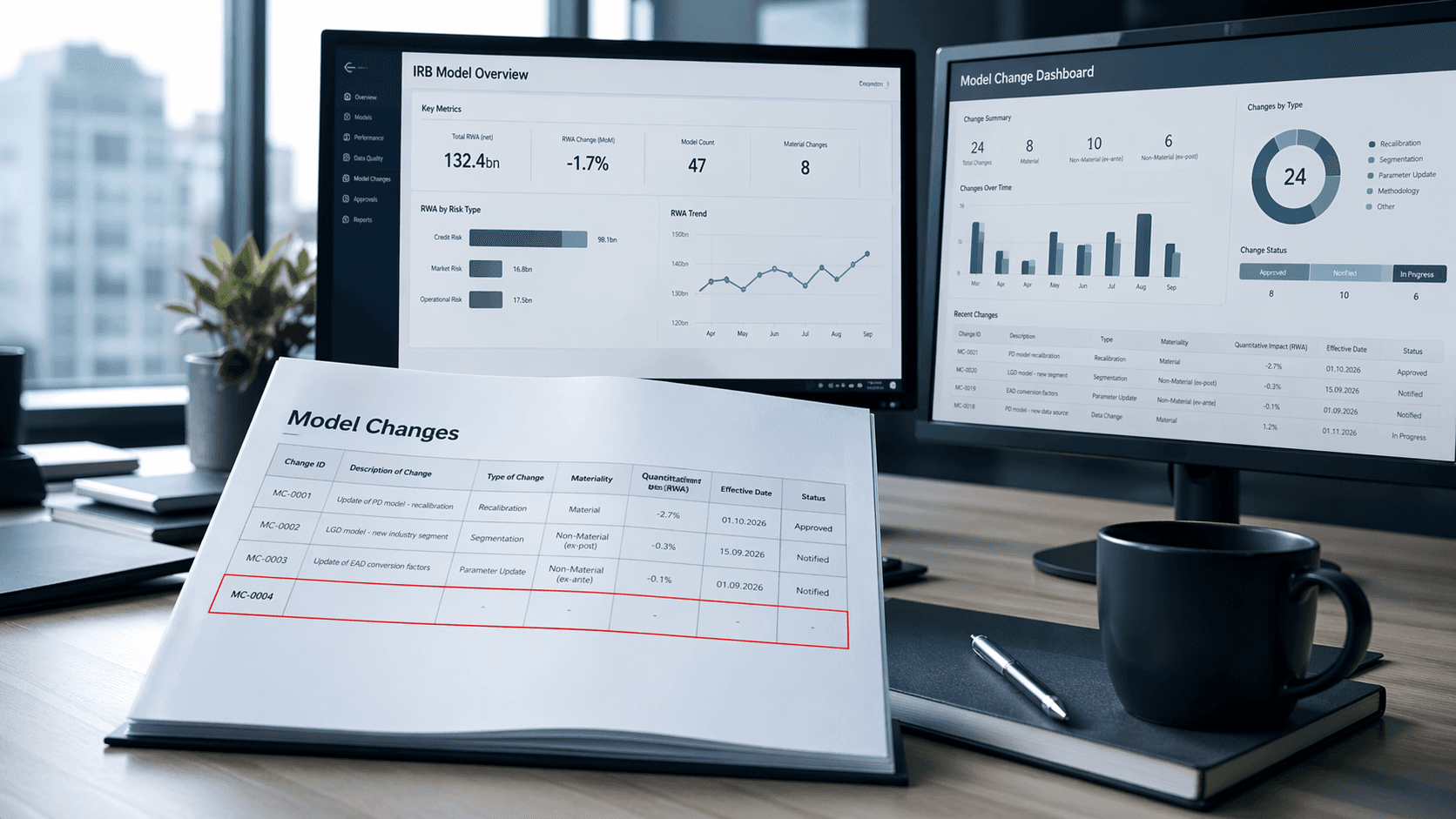
Less & Faster IRB Model Changes — What Actually Changed (and Why It Matters)
How the new IRB rules transform many previously time-consuming model changes into simple notifications—thereby drastically shortening approval times and significantly accelerating implementation

ESG Dashboard: Structure, KPIs & Tools for CSRD Sustainability Reporting
An ESG dashboard makes sustainability performance visible and auditable. This guide covers essential environmental, social, and governance KPIs, CSRD/ESRS alignment, data collection strategies, and tool selection for organizations building audit-ready ESG reporting.